Filip Mikuš and Jakub Obetko at the SecTec Security Day 2018 Conference
Our Security Specialists Filip Mikuš and Jakub Obetko represented Aliter Technologies at the SecTec Security Day 2018 with a presentation focused on security systems and events management (SIEM).
The goal of the lecture was to outline to a wide audience how to teach SIEM “good behaviour”. Since the centralized view on IT systems is becoming more and more popular in regards to IT infrastructures, the need to secure and implement multiple security tools in the system is growing.
SIEM allows users to perform effective surveillance and accelerate the detection and resolution of security incidents. Unfortunately, after implementation, SIEM is perceived as a preloaded log collector and an adherence for administrators. The presentation of our specialists provided useful tips and tricks based on their own experience of how to proceed with the deployment of SIEM to enhance the security of the systems most effectively.
Mohlo by vás zaujať
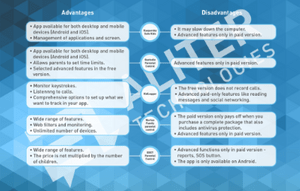
How to monitor what they are watching, what they are reading, who they are communicating with? One of the useful helpers for the protection and saf...
February 6th is Safer Internet Day. The aim of this day is to raise awareness of a safer and better internet for everyone, and especially for child...
Qubit Conference® 2023 with our participation!
In addition to the police, a unique monitoring system oversees the safety of hundreds of politicians, diplomats and presidents, which monitors and ...